The more connected things are, the more vulnerable they become. This truism of cybersecurity has profound implications for the Internet of Things that’s just around the corner—and for the energy grid that will power it.
That smart thermostat, video doorbell, or Amazon Echo you’ve set up in your home provides just a foretaste of what’s ahead for both consumers and industry.
 “As more products and pilot programs become available, a lot of people already have the bare bones of an Internet of Things,” says Shalinee Kishore (photo), a professor and Iacocca Chair of Electrical and Computer Engineering who serves as co-director of Lehigh’s Institute for Cyber Physical Infrastructure and Energy (I-CPIE.) “With the advent of 5G cellular, we’ll see far more people and industries participating in a matter of a few years.”
“As more products and pilot programs become available, a lot of people already have the bare bones of an Internet of Things,” says Shalinee Kishore (photo), a professor and Iacocca Chair of Electrical and Computer Engineering who serves as co-director of Lehigh’s Institute for Cyber Physical Infrastructure and Energy (I-CPIE.) “With the advent of 5G cellular, we’ll see far more people and industries participating in a matter of a few years.”
With the IoT, as it’s known, all manner of devices, appliances, and equipment will communicate and interact not only with each other but with the power grid. The grid in turn will become smarter—meaning both attuned to information and demands throughout its networks and able to respond nimbly, efficiently, and reliably to changes in the flow of energy, data, and money.
Cyber systems have become critical for monitoring the grid, both to understand what’s happening system wide and to respond to troubles—traditionally physical—like downed power lines or failed equipment.
“Now cyber systems that shore up the grid are also points of vulnerability,” Kishore says. “Instead of attacking equipment, malicious agents could attack the cyber systems that monitor and control electricity. The grid ran for decades without cybersecurity concern, but there’s a new layer of complication that you get by making the grid smarter.”
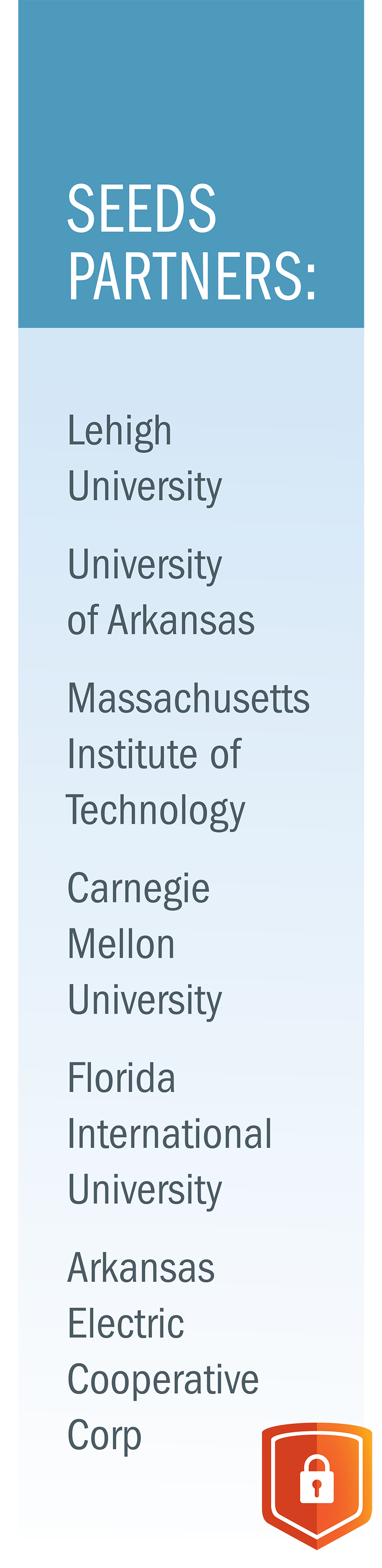
Concern about cybersecurity for energy systems led the Department of Energy to fund a five-year grant shared by Lehigh and four other universities in conjunction with industry partners to research various aspects of cybersecurity for energy delivery. The work is coordinated through a joint Cybersecurity Center for Secure Evolvable Energy Delivery Systems (SEEDS) spearheaded by the University of Arkansas.
Lehigh is now past the midway point of its $3.5 million grant but is focused on interconnected cybersecurity research that goes far beyond the scope of the DOE project. (SEEDS may continue with industry support after federal funding expires.)
Cyber Lies
A cyberattack on the grid would likely seek to cause power failures. Disrupting electricity flow can damage equipment, possibly leading to further outages or even cascading blackouts. Beyond causing social and business turmoil, such failures have the potential to endanger lives. By cutting power to health care facilities or sick people who rely on medical equipment at home, or by directly harming utility workers handling equipment that’s damaged, overloaded, or mistakenly thought to be turned off, bad actors could wreak real havoc on a community.
But attacks could play out in a variety of ways. Data falsification is one threat. Attackers may implant data that make the grid look like it’s running fine when it’s not—or has problems when it doesn’t.
“Either way, falsified data can mislead operators and prompt them to take incorrect measures that could disrupt electrical flow and damage equipment,” Kishore says.
Cyber lies could also wreak havoc with economic transactions tied to swings in supply and demand. One scenario involves what’s known as locational marginal prices. LMPs allow the cost of wholesale electricity to reflect the value of energy at different locations in the grid based on patterns of generation, load, and physical limits on the transmission system. The interplay is a bit like using a taxi or Uber: Travel costs—whether for riders or megawatts of electricity—are relatively low when it’s easy to get from one point to another but become pricier when demand surges and/or the route congests.
Price fluctuations can prompt electricity consumers to seek a financial payoff by withholding demand when energy costs appear high—like a rider who opts to travel outside of rush hour. This concept, called demand response, will increasingly become available to consumers as a feature of the smart grid. An attacker who falsifies energy pricing could throw off financial balances—or trigger surges of energy into lines and equipment that are dangerously unprepared for them. Incorrect exchanges could lead to losses or disturbances with a variety of serious consequences.
Experts like Blum—who was named a 2018 IEEE Signal Processing Society Distinguished Lecturer and speaks often on cybersecurity topics—believe the greatest cyberattack dangers may lie outside the grid.
Energy industries are highly regulated and very careful about what they do. In fact, cybersecurity research in the energy sector can be challenging because grid operators are often reluctant to share real-world data about how their systems actually behave.
“I’m much more worried about commercial applications of Internet of Things systems,” he says. “These are much less protected. Who will provide security, and how? Will manufacturers do it? This is much less clear.”
He cites the example of rapidly developing driverless cars, which include technologies familiar to Lehigh researchers and students such as systems for communications, radar, sensor processing, and statistical decision making. It’s known that radar systems of interest to car manufacturers can be cyberattacked. So can GPS.
“It’s not hard to spoof a GPS system,” Blum says. “The signals are completely known, and nearly any electrical engineering undergraduate could build a fake GPS transmitter very easily and inexpensively.”
Biomedical devices are another example. In an IoT world, sensors in the body might monitor health and find problems early. Sensors might even convey information to tiny smart devices in the body capable of fixing problems before they become severe.
“Imagine if these kinds of systems are cyberattacked,” Blum says. Driverless cars might be hijacked for terrorist strikes—perhaps remotely. Drones could be at risk in similar ways. Attacks on medical devices could taint health data or interfere with function.
Vulnerabilities in commercial Internet of Things systems could also work back to the grid. Imagine that your home becomes a cyber physical system in which smart devices make decisions—based on your preferences or behavior—about lighting, temperature, and appliance use guided in part by demand response to energy use throughout the grid.
“All these systems are interdependent,” Kishore says. “In effect, each device can become a portal to the larger network. You buy a device off Amazon and you don’t know about its design and manufacturing. It might have serious security holes. If an attacker finds one hole in one device, every person using that device can potentially cause problems with the smart grid.
 Layered Protection
Layered Protection
Cybersecurity defenders work at a disadvantage. “We have to assume attackers have infinite time and resources, and could strike at any moment,” Kishore says. “Defenders, on the other hand, have limited time and resources, and no warning.” Given the multitude of malicious possibilities, no single security approach can be relied upon.
“We’re looking at providing many layers of protection,” Blum says. “Some are well known ways to keep people out of the system like firewalls and encryption. At Lehigh we’re looking at new approaches. Among them are methods of thwarting attacks even if bad actors breach a system.”
One approach is to build on the wealth of data provided by constant measurement.
“This is the way the grid is going,” Blum says. “We have a lot of sensors monitoring voltage, current, power flow, and a wide variety of other variables at any given time. Historical data—including past energy usage patterns, weather conditions, and system configurations under specific circumstances—can be used to produce mathematical models of how the grid should look in different situations. When combined with current sensor measurements, anomalies stand out.”
“If somebody gets into the system and tries to issue commands for certain things to happen, we can realize these commands don’t make sense,” he continues. “Given enough data and measurements to pool with machine learning algorithms, we can judge what is reasonable and what is inconsistent or an outlier.”
This may become important for shoring up vulnerabilities introduced with greater reliance on renewable energy sources such as the sun or wind.
“With renewables, the supply-side grid looks very different than when a coal plant just generates whatever kilowatts are needed,” Kishore says. Wind and solar generation are inherently volatile, surging and waning with the weather—an opportunity for attackers exploiting uncertainty to make false data look real.
“We’re developing algorithms to find data injection attacks that mimic renewable generation,” Kishore says. “Imagine that a wind farm connected to a power line typically generates 10 to 10.5 megawatts. An output of 9.6 megawatts may seem reasonable, given the variability. But by using machine learning algorithms, we can hone that judgment through probabilistic forecasting. The probability distribution shows that a 9.6 megawatt reading actually is not probable; the algorithm tells you that something doesn’t seem right.”
 Time Bandits
Time Bandits
Identifying inconsistencies—or understanding anything about how a system is working now or has worked in the past—requires the entire system to agree on what time it is. GPS can be used for timekeeping, as can a widely used standardized protocol known as IEEE 1588. This protocol efficiently sets clocks throughout a system by having them synchronize via communication channels with a relatively small number of master clocks.
“We understand how someone could get into the system and conduct time-synchronization attacks,” Blum says. “Such attacks wouldn’t need to falsify data—just delaying sensor measurements could prove highly disruptive in IEEE 1588. We now have algorithms that allow systems to keep time accurately even if they’ve been attacked.”
“Timekeeping protection has value beyond power systems,” he continues. “What we’re doing is significant for a variety of applications, including cellular base stations. Cellular devices are now able to talk to several base stations at the same time, so clocks in those systems need to be highly accurate.”
Cybersecurity will continue to be important for broader arrays of technology as they increasingly become connected. Interdependencies are growing even between energy industries.
“A third of electrical generation now comes from natural gas,” Kishore says. “Plants that convert natural gas to electricity are connected to two grids—gas and electricity—at the same time, and this interdependency introduces vulnerabilities all its own. Even if the electrical grid is protected, it has security holes through the natural gas network, which is more localized and fragmented. We’re looking at cybersecurity between the two from many angles, starting with communications systems—what’s needed, how to make them secure, and what they would look like under different policy scenarios.”
Such blended issues play to Lehigh’s strengths.
“We’re able to look at policy, market, and technology solutions with both a wide view and deep expertise through various disciplinary and methodological approaches,” Kishore says. “It’s the whole gamut required to address cybersecurity for large-scale systems.”
Story by Richard Laliberte